Authenticate a Customer
An access token is required before an application can access Cortex. To validate the end user’s credentials, the client application can request a registered user access token. This token enables access to resources that require a registered account and resources that do not require registered accounts.
Requesting an access token
Below is an example of the authentication workflow for requesting a REGISTERED access token from the client application’s perspective.
Construct a
POSTrequest to the OAuth2 Resource and set the content-type toapplication/x-www-form-urlencodedPOST http://www.myapi.net/oauth2/tokens Content-Type: application/x-www-form-urlencodedInclude the following parameters in the request body:
grant_type=password&username=oliver.harris@elasticpath.com&password=password&scope=mobee&role=REGISTEREDCortex authenticates the request and returns either a success or failure HTTP response.
Successful authentication returns the following HTTP response:
{ "access_token": "c7326d79-9273-4820-b45d-587f90d1dc9b", "token_type":"bearer", "expires_in": 359, "scope" : "MOBEE", "role": "REGISTERED" }Unsuccessful authentication returns a
401 Unauthorizedstatus code and an error message.
Using an access token
Once the token is granted, all subsequent requests to Cortex must include the access token in an Authorization request header. If the access token is invalid, does not exist in the Authorization request header, or the user does not have the authority to access a resource, Cortex returns a 401 Unauthorized status code
Add the access token to your request headers as shown in the example below:
Content-Type: application/json
Authorization: Bearer c7326d79-9273-4820-b45d-587f90d1dc9b
Token Type
You must use Bearer in the Authorization header. This is an OAuth 2.0 standard.
Revoking an access token
Revoke an access token by calling DELETE on the OAuth2 Resource. Include the access token to revoke in the Authorization request header.
DELETE http://www.myapi.net/oauth2/tokens
Authorization: Bearer c7326d79-9273-4820-b45d-587f90d1dc9b
Access token validity and expiration
Access tokens are immediately valid once they are returned to the client application. Tokens are valid for 1 week, after which they expire and are no longer valid for access.
Sample OAuth2.0 Authentication Application
We recommend using a client library to handle OAuth 2.0 authentication instead of handling the implementation yourself. The sample code below is for demonstration purposes only, this is not production ready code. The sample code is written using jQuery.
The example starts with the authentication form that captures the required information from the end-user.
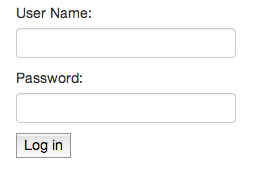
Once the user clicks the 'Log In’ button, the oAuthSubmit function sends the user’s credentials to the OAuth2 resource. If authentication is successful, a successful JSON response is returned to the client with the token in the body of the response. In this example, the client attaches the string 'Bearer’ to the token when it’s persisted. Bearer is an OAuth 2.0 standard and is required when the token is used to access protected resources.
For more information, see Using an access token above. The client application also authenticates user’s with it’s current scope and as a registered customer
